When you choose to run your kubernetes cluster on AWS, there are 2 easy ways:
The common thing between both ways, is using Amazon ECR for storing the docker images and have a worry free push, pull to and from Amazon ECR which requires a IAM Role that allows the worker nodes pulling the images saftly.
Amazon ECR
Amazon Elastic Container Service is one of the cheapst ways to store docker images and safer due to the nature of Amazon IAM. To pull from ECR you first need to authenticate using you AWS credentials, or role, get a token, do docker login to your ECR with the server address, and pull from the repository the docker image.
Seems hard, well it’s not that bad. Let’s do a short walkthrough from scratch assuming you are on a Mac
# Install awscli
brew install awscli
# Configure awscli
awscli configure
# Follow the configuration prompt putting your Access key and Token, this will create a ~/.aws/credentials file with your credentials
# Login to your ECR in the needed region
$(aws ecr get-login --no-include-email --region eu-west-2)
# This will get the docker login ready with the username, token and registry URL and will execute it.
If everything went ok, then you should get these lines:
WARNING! Using --password via the CLI is insecure. Use --password-stdin.
Login Succeeded
So now you are able to pull and push to ECR, assuming you have the proper permissions.
There are builtin AWS Policies for read only
AmazonEC2ContainerRegistryReadOnlyFor read and writeAmazonEC2ContainerRegistryPowerUserAnd for read, write and deleteAmazonEC2ContainerRegistryFullAccessIf you have more limitation needed, a specific region or something else, copy the policies and limit on new ones.
Docker for Mac
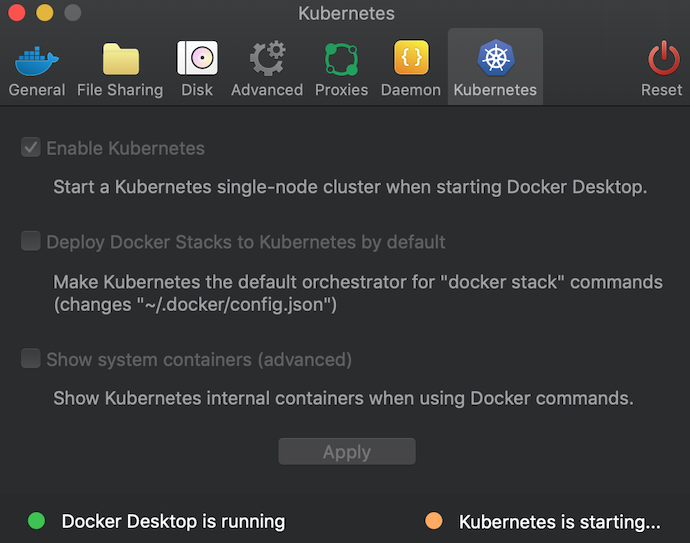
So, now that we have all ready, lets install docker After installation click the docker icon and select Prefrences and enable Kubernetes and click apply
Pulling docker images
So, now we have a running docker and kubernetes, and we are ready to pull images from ECR, and I’ts quite easy :) I’ve made a short script that generates a registry-secret named ECR that I can use to pull images
#!/bin/bash
# Set your AWS region
REGION="us-west-2"
# Get ECR login token
TOKEN=$(aws ecr get-login-password --region $REGION)
# Create kubernetes secret for ECR
kubectl create secret docker-registry ecr \
--docker-server=${AWS_ACCOUNT_ID}.dkr.ecr.${REGION}.amazonaws.com \
--docker-username=AWS \
--docker-password=${TOKEN} \
--docker-email=none@email.local
echo "ECR secret created successfully"
- Make sure to set the proper region
- Make sure to be in the right kubectl context
Now, we have set in the default Kubernetes namespace a registry secret that allows to pull docker images from ECR, this secret contains the temporary token that AWS API responded with. so, if you have a long running cluster on your machine, you will need to delete and recreate it once the token expired.
AWS Credentials secret
Now let’s make another generic secret containing our AWS credentials with another easy bash script
#!/bin/bash
# Create AWS credentials secret
kubectl create secret generic aws-credentials \
--from-literal=aws-access-key-id=${AWS_ACCESS_KEY_ID} \
--from-literal=aws-secret-access-key=${AWS_SECRET_ACCESS_KEY} \
--from-literal=aws-region=${AWS_DEFAULT_REGION}
echo "AWS credentials secret created successfully"
And now we can deploy any docker image in our ECR that uses aws credentials (On AWS use Roles and not credentials if possible) named aws_credentials.
Sample app deployment from ECR to local Kubernetes
So my yaml deployment will now look like this:
apiVersion: apps/v1
kind: Deployment
metadata:
name: my-app
spec:
replicas: 1
selector:
matchLabels:
app: my-app
template:
metadata:
labels:
app: my-app
spec:
containers:
- name: my-app
image: 123456789012.dkr.ecr.us-west-2.amazonaws.com/my-app:latest
ports:
- containerPort: 8080
env:
- name: AWS_ACCESS_KEY_ID
valueFrom:
secretKeyRef:
name: aws-credentials
key: aws-access-key-id
- name: AWS_SECRET_ACCESS_KEY
valueFrom:
secretKeyRef:
name: aws-credentials
key: aws-secret-access-key
- name: AWS_DEFAULT_REGION
valueFrom:
secretKeyRef:
name: aws-credentials
key: aws-region
imagePullSecrets:
- name: ecr
Enjoy your running application on your local Kubernetes cluster pulled from ECR and uses AWS Credentials.